Iowa Cybersecurity Laws in 2026: What Businesses Need to Know
Iowa cybersecurity laws in 2026: breach rules, data privacy, and what businesses must do to stay compliant.
When Does Your Business Need a Hardware Refresh Cycle?
A hardware refresh cycle isn’t just an upgrade — it’s a business decision that affects productivity, security, and risk. Performance issues, unsupported systems, and growth are clear signals it may be time to plan proactively rather than react to failure.
Responsibility: Privacy Doesn’t End at Recycling

Data privacy doesn’t end at recycling. Responsible recycling ensures secure handling, chain of custody, and verified data removal—protecting people and the planet.
When Data Doesn’t Go Away: Why Intentional End-of-Life Decisions Matter

Data doesn’t disappear when devices are deleted, broken, or reset. Intentional sanitization or destruction is the only way to stay secure.
Preservation: Keeping the Data You Still Need

Data security isn’t deleting everything. Preservation means securely backing up and protecting the data you still need as devices change or retire
Digital Footprint: Your Data Isn’t Just on Devices
Getting rid of a device doesn’t mean your data is gone. Emails, files, photos, and account details often live on in cloud backups, apps, and vendor systems long after hardware is retired. Forgotten accounts and automatic syncs create hidden risks that many people never see. Understanding your digital footprint means managing where data lives—not just where devices go.
Device Identification: You Can’t Protect What You Don’t See

Device Identification.
Untracked devices create hidden risks. Old laptops, servers, and phones can still hold sensitive data long after they’re out of use. Without proper identification, these devices become security and compliance blind spots.
Knowing what devices you have—and where they are—is the first step to protecting data and managing technology responsibly.
Easy Device Decommissioning in Iowa

Learn the difference between IT asset disposition vs recycling. Certified ITAD services protect your data, ensure compliance, and support sustainability—far beyond a basic recycler.
Why ITAD Services Matter More Than Recycling Alone
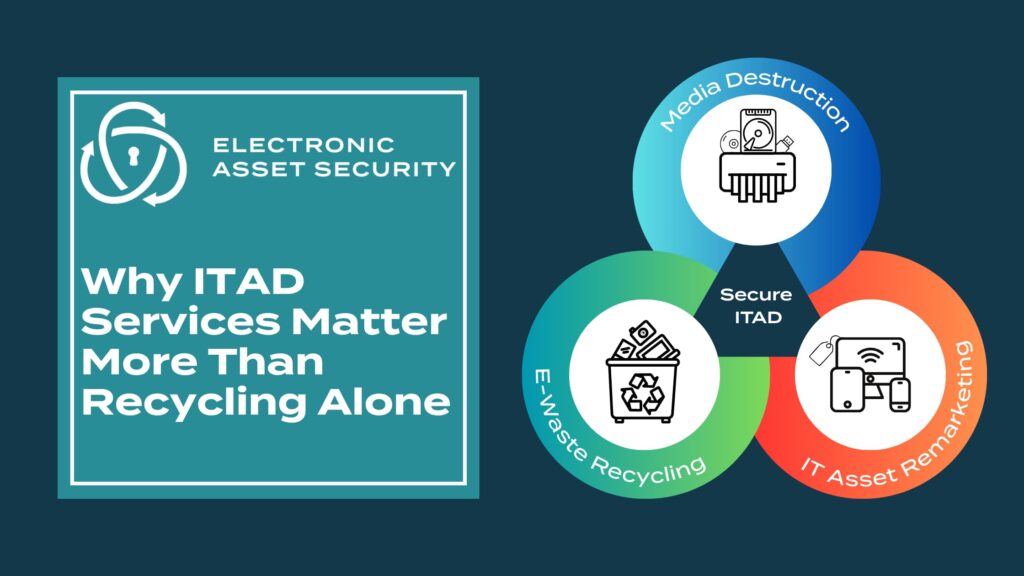
Learn the difference between IT asset disposition vs recycling. Certified ITAD services protect your data, ensure compliance, and support sustainability—far beyond a basic recycler.
The Hidden Cost of Improper Data Destruction | Secure IT Disposal

A drilled drive isn’t a destroyed drive. Learn the real cost of improper data destruction and why certified in-house shredding ensures total protection.
